Thabet còn có hàng loạt cái tên khác là THA BET, THA hay THA CASINO, Thiên Hạ Bet. Đơn vị này hiện đang là cái tên sáng giá nhất trong là cá cược Việt Nam. Mọi sản phẩm giải trí từ casino, các cược, slot, xổ số… mà họ đem đến đều đảm bảo tiêu chí công bằng – luật chơi đơn giản – tiền thưởng khủng.
Vì sao bạn nên lựa chọn nhà cái Thabet ?
Kể từ khi hoạt động đến nay thabet luôn đảm bảo hoạt động theo đúng tôn chỉ. Đảm bảo đem đến cho khách hàng Việt Nam môi trường giải trí hiện đại, hấp dẫn và cực kỳ an toàn.
Cho dù rất nhiều đối thủ đã ra đời nhưng vẫn không thể cạnh tranh được với Thabet. Và thương hiệu này luôn là sự lựa chọn hàng đầu của các cược thủ.
LỊCH BẢO TRÌ THABET - THA CASINO hôm nay 23/04/2024
| Thời gian | Nội dung bảo trì |
|---|---|
| 4:45 | SA Casio bảo trì hoàn tất. |
| 5:18 | SCB Ngân hàng bảo trì hoàn tất, nạp rút mở. |
| 12:38 | KU Thể Thao và Cool-In-Live bảo trì hoàn tất, xin lưu ý! |
| 16:18 | Pinnacle Sports bảo trì hoàn tất. |
| 17:13 | Sảnh SABA Esport bảo trì hoàn tất. |
| 22:58 | Ngân hàng TPB bảo trì đột xuất đã hoàn thành, nạp rút mở. |
Giao diện tha casino hiện đại, đẳng cấp, thân thiện

Ngay từ khâu thiết kế, nhà cái đã phải cố gắng nghiên cứu thật kỹ để đưa đến cho khách hàng một giao diện thân thiện, dễ dùng nhưng vẫn đầy đủ các tính năng. Đến với nhà cái Thabet người chơi không hề gặp bất cứ lúng túng trong thao tác nào. Vì mọi thứ đều có chỉ dẫn cụ thể.
Không những thế nhờ sự kết hợp với bố cục, màu sắc và đồ họa đẳng cấp mà game thủ luôn có được những trải nghiệm hòan hảo bậc nhất. Dù là trên website hay bản app dành riêng cho thiết bị di động đều cực kỳ thông minh và hữu ích.
Nhà cái uy tín bậc nhất thabet
Được cấp phép hoạt động ngay từ khi mới ra mắt đến nay, mặc dù đã trải qua nhiều năm làm việc. Nhưng nhà cái chưa hề dính bất cứ thông tin xấu nào liên quan đến lừa đảo, thiếu uy tín.
Mọi hoạt động của Thabet đều đặt dưới sự kiểm soát gắt gao của các cơ quan quản lý có thẩm quyền. Vì thế khách hàng hoàn toàn có thể yên tâm 100% về vấn đề pháp lý của trang cá cược trực tuyến này.
Bên cạnh đó, họ còn có đội ngũ nhân viên chăm sóc khách hàng hết sức tận tâm, luôn làm việc 24/24. Mọi câu hỏi, thắc mắc, các vấn đề người chơi cần giải đáp sẽ xử trong thời gian ngắn nhất.
Không những thế, Thabet cùng nhà cái Kubet còn là đối tác, nhà tài trợ cho nhiều đội bóng lớn trên thế giới như:
- CLB Aston Villa.
- Leicester City.
- CLB Wolverhampton Wanderers F.C.
Điều này càng khẳng định được giá trị thương hiệu và mức độ uy tín của nhà cái.
Tha casino Cá cược thể thao đẳng cấp châu Á
Cá độ bóng đá chỉ là một trong nhiều hoạt động cá cược thể thao đang có mặt tại nhà cái Thabet. Đến đây ngoài bóng đá, các bạn còn dễ dàng tìm cho mình được kèo cược hấp dẫn ở những bộ môn khác như: Bóng chày, bóng bàn, bóng rổ, Tenis, đua ngựa…
Nhà cái luôn nỗ lực đem đến nhiều kèo cược ngon ăn nhất. Đồng thời, cố gắng đa dạng hóa sản phẩm cá độ để phục vụ nhu cầu của mọi khách hàng.
Hiện nay, nhà cái có nhiều sảnh cá độ hấp dẫn như: CDM, IB, JZ, BET, AG,… Mỗi sảnh lại có ưu điểm và sức hút riêng. Hàng trăm thể loại kèo khác nhau từ truyền thống cho đến mới lạ như: Kèo châu Á, kèo châu Âu, kèo Tài – Xỉu, kèo thẻ vàng, kèo phạt góc, kèo hiệp 1… đang chờ đón bạn tại Thabet.
Thabet Casino online đỉnh nhất Đông Nam Á
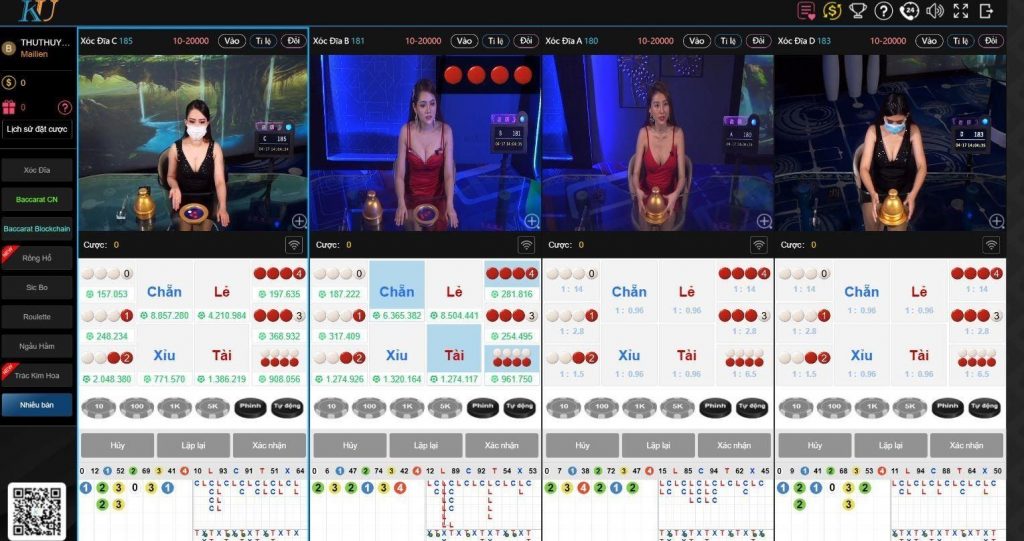
Bước chân vào sảnh Casino của Thabet người chơi sẽ cảm nhận được sự khác biệt. Đầu tiên là giao diện được thiết kế đẳng cấp, bối cảnh ở mỗi bàn chơi đều tương tự các sòng bài lớn ở Ma Cao, Hong Kong, Las Vegas…
Thứ 2, dàn chia bài hay còn gọi là Dealer đều được đào tạo bài bản. Họ không chỉ có vẻ ngoài xinh đẹp, quyến rũ mà còn rất am hiểu kiến thức về Casino.
Bên cạnh đó, Thabet còn là đối tác lớn của nhiều nhà phát hành game hàng đầu thế giới như: WM, BBIN, AG Gaming, GPI – SA – AES… Nhờ thế mà các trò chơi vô cùng đa dạng. Trên thị trường nhà cái có tựa game casino nào thì ngay lập tức nó có mặt tại Thabet.
Lô đề – xổ số tỷ lệ ăn cực cao
Để khách hàng Việt dễ tiếp cận với lô đề trực tuyến, nhà cái đã “bê nguyên” lối chơi lô đề, xổ số truyền thống lên sảnh này. Nhờ thế khách hàng không cần tìm hiểu mà có thể tham gia bất cứ lúc nào. Không những thế tỷ lệ ăn của nhà cái Tha Bet còn cao hơn so với mức truyền thống nâng từ 1 ăn 80, lên 1 ăn 99 thậm chí là 99.5.
Các chuyên mục uy tín của thabet đó là
- Soi cầu xsmb có độ chính xác rất cao
- Dàn đề ăn thông liên tiếp
Nổ hũ tha casino
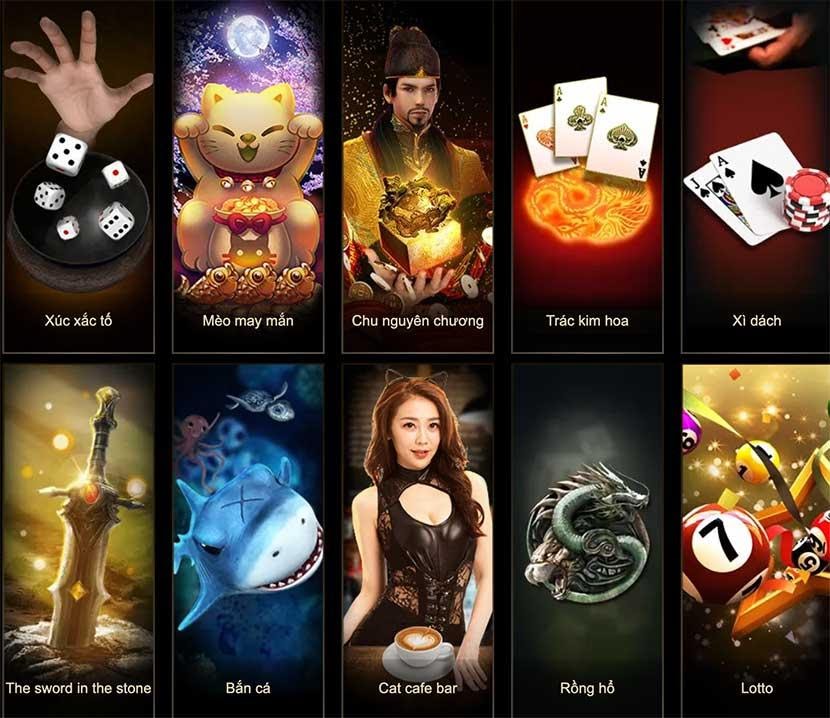
Kho nổ hũ của Thabet có hơn 500 đầu game chia thành nhiều sảnh lớn như Sảnh MG, Sảnh AG, Sảnh HB… Đảm bảo người chơi có thể tìm được trò mà mình thích nhất. Lối chơi siêu đơn giản dễ ăn tiền với giải thưởng Jackpot lên đến 3 tỷ.
Soi cầu thabet
Hỗ trợ khách hàng soi cầu 3 miền siêu hấp dẫn.
Nhóm VIP Thabet
Dành riêng cho mọi khách hàng, tham gia nhóm bạn nhận được rất nhiều quyền lợi.
10 điểm ưu việt của Thabet
- Giao diện thông minh, hiện đại.
- Trò chơi hấp dẫn, phong phú, đa dạng.
- Sử dụng trên nhiều nền tảng, thiết bị.
- Đăng ký tài khoản siêu nhanh.
- Nạp rút tiền siêu tốc.
- Tỷ lệ cược, tỷ lệ ăn cực cao.
- Trả thưởng “nhanh như chớp”.
- Chăm sóc khách hàng tận tình.
- Nhiều khuyến mãi.
- Bảo mật an toàn tuyệt đối.